Protect Operations, Customers, Investors and Employees with Dynamic, Compliant Security Processes that Teach Every Computing Endpoint
As threats continue to evolve and multiply, total infrastructure security is increasingly difficult to maintain. The proliferation of network access points, mobile computing devices and shared business processes only adds to the concerns. To support operations and enterprise security, IT professionals must deal effectively and efficiently with network access requirements, identity management and regulatory requirements.
Say hello to a company who will help you architect strong Information Security Management Systems
Hi-Link offers expert security services and solutions that leverage proven technologies to address near-term threats and vulnerabilities. We also place a high priority on helping enterprises develop and deploy cohesive security policies throughout their organizations, to proactively address enterprise security challenges and meet the challenge of compliance with multiplying regulations.
Cyber Security consulting services design and architect solutions to protect the enterprise. Once the solution has been established we engineer and integrate the solution to operate within the enterprise. After the solution is operational we validate and verify that the solution is providing the protections as intended.
Cyber security advisory solutions are designed to inspect, examine, and test the security controls applied within your enterprise and its components. Cyber Security Services provide detailed reports of weaknesses and findings based upon risk or other customized data. The data contained within the reports helps ensure compliance, reduce liability, mitigate risks and allows for resource allocation for issue remediation.

- Email & Content Data Security
- Endpoint and Mobile Security
- Network Security
- Application and Mobility Security
- Data and Big Data Security
- Advance Threat Protection - Zero Day
- IAM - Identity and Access Management
- Cloud Security
At a time when cybercrime, malware and damaging viruses are increasing exponentially each day, security is among the most vital aspects of your business computing needs. Network security does not just encompass outside threats, it also includes employee misuse of your network resources, which often creates additional avenues for security breaches and costly malware attacks.
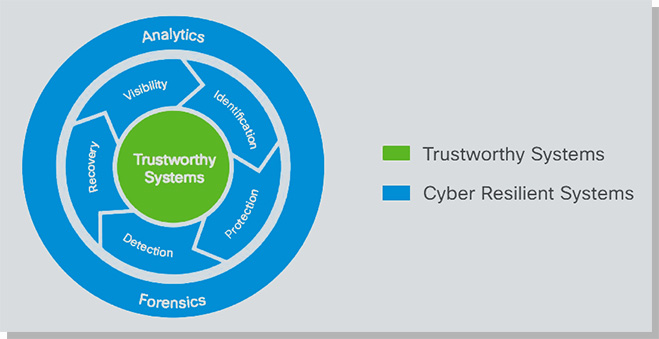
Securing your network requires visibility into how it’s being used so you can maximize bandwidth efficiency, minimize security threats and improve employee productivity. When breaches do occur, you must be able to quickly identify and contain them, and then take swift action to minimize any damage and avoid a similar intrusion in the future.
The Security Cycle to a Protected Network